### Outline
1. **Introduction**: Defining the “Infrastructure-Social” feedback loop and why decentralization is the bedrock of digital sovereignty.
2. **Key Concepts**: Understanding the distinction between the application layer (social logic) and the infrastructure layer (the “pipes”).
3. **Step-by-Step Guide**: How to evaluate the decentralization profile of a technology stack.
4. **Real-World Applications**: Analyzing decentralized storage (IPFS/Arweave) and compute (DePIN) as pillars for social applications.
5. **Common Mistakes**: The trap of “decentralization theater” and over-reliance on centralized RPCs or cloud providers.
6. **Advanced Tips**: Implementing verifiable computation and sovereign identity to harden the stack.
7. **Conclusion**: The necessity of aligning technical architecture with human-centric values.
***
The Decentralization of Infrastructure: Why the Foundation Defines the Future
Introduction
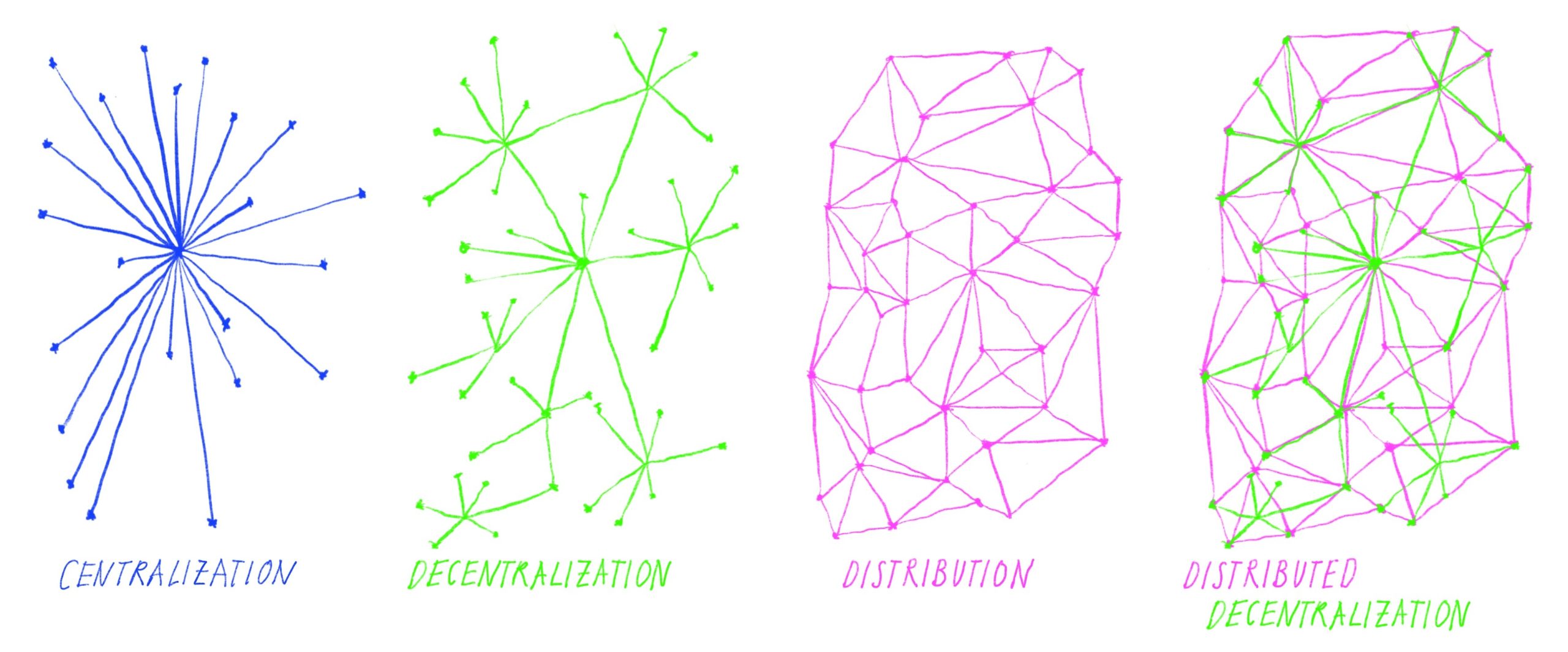
For years, the discourse surrounding decentralization has focused almost exclusively on the “social logic”—the governance models, tokenomics, and community-driven applications that define Web3. While these elements are vital, they often obscure a fundamental reality: a decentralized social layer cannot survive on a centralized infrastructure. If your decentralized application is built on top of AWS, relies on centralized domain name registries, or uses proprietary, opaque APIs, the social logic is merely a facade.
The decentralization of the infrastructure layer is not a luxury; it is a prerequisite for digital sovereignty. When we talk about “infrastructure,” we are referring to the underlying protocols, storage layers, compute nodes, and network connectivity that allow data to persist and programs to execute. Without decentralizing these, you are simply building a digital castle on rented, easily sabotaged land. This article explores why the “pipes” of the internet must be as resilient as the social structures they support.
Key Concepts
To understand the necessity of infrastructure decentralization, we must first distinguish between the two layers of the modern tech stack: the Application Layer and the Infrastructure Layer.
The Application Layer is the user-facing side of the internet. It is where social logic resides—the rules for how people interact, how content is moderated, and how value is exchanged. When this layer is decentralized, users are theoretically empowered to govern their own digital spaces.
The Infrastructure Layer is the “silent” architecture. It includes storage (where your photos and posts live), compute (where the logic of your code is processed), and the network (how information travels from point A to point B). If the infrastructure is centralized, the owner of that infrastructure holds “kill-switch” power. Even if your social protocol says you own your data, if a centralized cloud provider deletes the server hosting that data, your ownership is effectively nullified.
True decentralization requires that the infrastructure be as resistant to censorship and failure as the social applications it sustains. If the foundation is brittle, the entire structure is subject to the whims of a central authority.
Step-by-Step Guide: Evaluating Your Technology Stack
If you are building or evaluating a decentralized project, use this framework to determine if the infrastructure matches the ambition of the social logic.
- Identify Dependency Nodes: Audit your stack to find every point of failure. Are you using a centralized gateway (like Infura or Alchemy) to talk to the blockchain? If that provider goes down, your app goes dark.
- Audit Storage Persistence: Determine where user data is stored. If it is on a standard AWS S3 bucket, it is not decentralized. Transition toward verifiable, content-addressed storage solutions like IPFS or Arweave.
- Analyze Compute Locality: Determine where your smart contracts or decentralized app logic executes. Are you relying on centralized cloud instances for backend processing? Seek out decentralized compute networks (DePIN) that distribute processing across global, permissionless hardware.
- Verify Data Sovereignty: Ensure that users hold the keys to their own data. Can a user migrate their entire profile and history to a different interface without your permission? If not, the infrastructure is still locked behind a proprietary gate.
Examples and Real-World Applications
The shift toward decentralized infrastructure is best illustrated by the emergence of DePIN (Decentralized Physical Infrastructure Networks) and decentralized storage protocols.
Decentralized Storage (Arweave/IPFS): Consider a social media platform that uses Arweave for content storage. Unlike a traditional platform where a company can delete a “controversial” post, Arweave provides permanent, immutable storage. The infrastructure ensures the content remains accessible regardless of the platform’s social policy, effectively decoupling the social interaction from the storage medium.
Decentralized Compute (Akash Network): Imagine an AI-driven social bot. Traditionally, this would run on a massive, centralized server farm. By migrating this logic to the Akash Network, developers can deploy workloads across a global marketplace of underutilized hardware. This prevents a single cloud provider from de-platforming the AI agent based on the content it generates.
These examples prove that when infrastructure is decentralized, the “social logic” becomes truly resilient. The technology becomes a utility rather than a product controlled by a corporation.
Common Mistakes
Even well-intentioned teams often fall into traps that undermine their goals. Awareness of these pitfalls is the first step toward building a truly sovereign stack.
- The “Decentralization Theater” Trap: Many projects claim to be decentralized but rely on centralized RPC nodes for 90% of their traffic. This creates a false sense of security; the app looks decentralized, but it is effectively a centralized app with a blockchain backend.
- Ignoring Metadata Centralization: You might store the “post” on IPFS, but if the “metadata” (who liked it, who commented, follower lists) is stored in a centralized SQL database, you have not achieved decentralization. The social graph must be as decentralized as the content itself.
- Over-reliance on “Easy” Cloud Services: Using managed services like AWS Lambda or Google Firebase is convenient, but these services come with proprietary vendor lock-in. Once you start building on these platforms, the cost of migrating to decentralized alternatives increases exponentially.
Advanced Tips
To push your infrastructure toward true decentralization, consider these advanced architectural shifts:
Implement Verifiable Computation: Instead of trusting a centralized server to execute a function, use Zero-Knowledge (ZK) proofs to verify that the computation was executed correctly. This allows you to outsource computation to untrusted parties without sacrificing the integrity of your social logic.
Adopt Sovereign Identity (DID): Move away from “Login with Google” or centralized database-backed accounts. Implement Decentralized Identifiers (DIDs) so that users carry their identity with them. This ensures that the user’s reputation and social graph are portable across any platform that supports the same standards.
Multi-Gateway Strategy: Never rely on a single gateway for your decentralized infrastructure. Build your client-side applications to fetch data from multiple providers or, ideally, to allow the user to point their client to their own node. This eliminates the “centralized gateway” as a single point of failure.
Conclusion
The decentralization of the infrastructure layer is the silent, essential work of the next decade. While the social logic of Web3—governance, community, and economic incentives—provides the “why,” the infrastructure provides the “how.” Without a robust, decentralized foundation, our social applications are merely temporary experiments subject to the whims of centralized gatekeepers.
By moving toward content-addressed storage, decentralized compute, and sovereign identity, we ensure that the internet remains a public utility rather than a collection of private fiefdoms. The goal is to build technology that functions regardless of who is in charge. When the pipes are decentralized, the social logic can finally flourish with the permanence and freedom it was designed to protect.
Leave a Reply