**Outline:**
1. **Introduction:** The shift from centralized trust to cryptographic verification.
2. **Key Concepts:** Defining digital signatures, public/private key infrastructure, and the role of immutability in reputation systems.
3. **Step-by-Step Guide:** The workflow of signing a transaction (Generation, Hashing, Signing, Verification).
4. **Real-World Applications:** Blockchain consensus mechanisms, decentralized identity (DID), and supply chain provenance.
5. **Common Mistakes:** Key management failures, lack of timestamping, and improper entropy.
6. **Advanced Tips:** Multi-signature (multisig) wallets, hardware security modules (HSMs), and threshold signature schemes (TSS).
7. **Conclusion:** The future of verifiable data integrity.
The Cryptographic Foundation: Why Every Transaction Requires a Digital Signature
Introduction
In the digital age, trust is no longer a human construct—it is a mathematical one. Whether you are dealing with financial assets, sensitive data, or reputation scores, the question is always the same: How do we prove that a specific action was initiated by the authorized party and that the data has not been tampered with? The answer lies in the cryptographic signature.
By requiring a unique cryptographic signature for every transaction, systems move away from vulnerable centralized databases toward a model of decentralized integrity. This process ensures that no entity can adjust a reputation score or alter a ledger entry without the corresponding private key. Understanding this mechanism is essential for anyone building, auditing, or participating in modern digital ecosystems.
Key Concepts
To understand why cryptographic signatures are the bedrock of transaction integrity, we must break down three fundamental components: Public/Private Key Infrastructure (PKI), Hashing, and Non-repudiation.
Public/Private Key Infrastructure: Every user in a cryptographic system possesses a key pair. The private key is a secret string of data used to sign transactions, while the public key is shared openly. Because the two are mathematically linked, a signature created with the private key can be verified by anyone using the public key, without revealing the private key itself.
Hashing: Before a signature is generated, the transaction data is passed through a hashing algorithm. This creates a “digital fingerprint” of the transaction. If even a single bit of that transaction is changed later, the hash will change, causing the signature verification to fail. This is the primary mechanism that prevents tampering.
Non-repudiation: This is the legal and technical guarantee that the author of a transaction cannot later deny having sent it. Because only the owner of the private key could have produced a valid signature, the signature serves as an irrefutable proof of intent.
Step-by-Step Guide
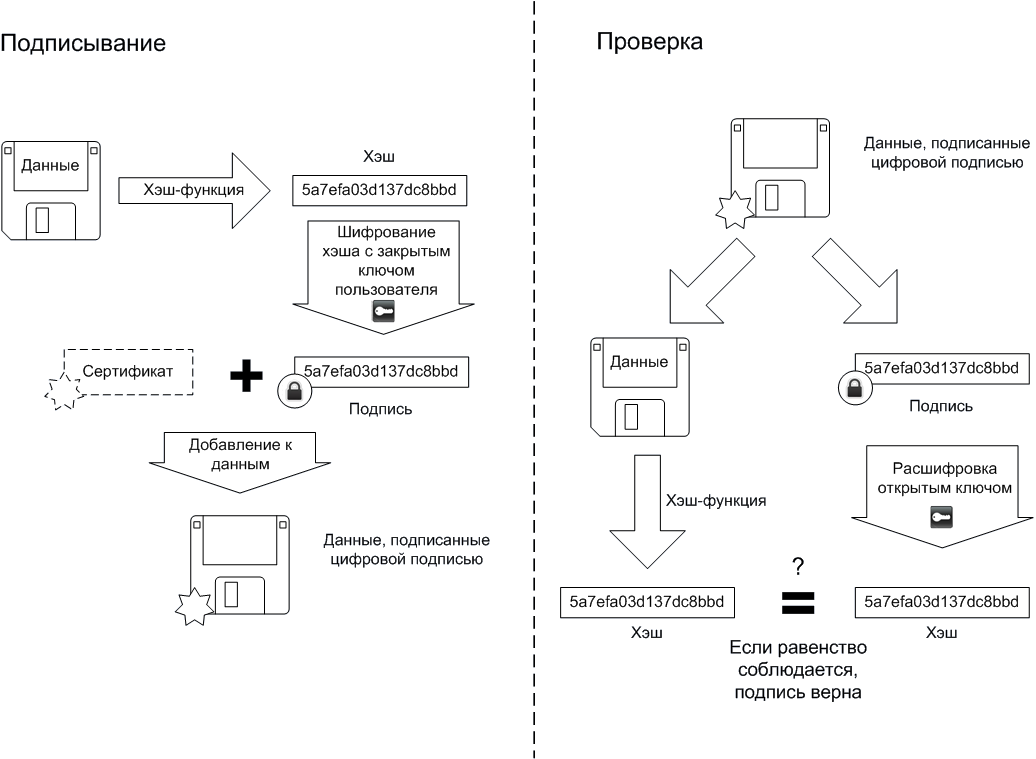
The process of signing a transaction happens in milliseconds, but it follows a rigorous logical flow to ensure security. Here is how a standard transaction is signed and verified:
- Transaction Construction: The initiator creates the transaction payload, which includes the sender’s address, the recipient’s address, the amount or data change, and a unique nonce (a number used once to prevent replay attacks).
- Data Hashing: The system takes the entire transaction payload and runs it through a cryptographic hash function (such as SHA-256). This results in a fixed-length string of characters.
- Signing: The user’s software uses their private key to encrypt the hash. This encrypted hash is the “digital signature.”
- Broadcast: The transaction, along with the signature and the sender’s public key, is broadcast to the network or the ledger system.
- Verification: The system receiving the transaction uses the sender’s public key to decrypt the signature. It then compares this decrypted hash with a fresh hash of the transaction data. If the two hashes match, the transaction is valid and immutable.
Real-World Applications
The requirement for cryptographic signatures extends far beyond simple cryptocurrency transfers. Its application is critical in any environment where reputation and data integrity are at stake.
Decentralized Identity (DID): In systems where users control their own reputation, a user might earn “trust points” for verifiable actions. By signing every action, the user ensures their reputation score is based on a verifiable chain of custody. No administrator can artificially inflate or deflate these scores because they lack the user’s private key to sign fraudulent entries.
Supply Chain Provenance: Imagine a pharmaceutical supply chain where every handoff requires a digital signature. When a drug moves from the manufacturer to a distributor, the manufacturer signs the transaction. If the drug is later found to be counterfeit, the ledger provides an immutable audit trail showing exactly where the chain of custody was broken or where an unauthorized entry was injected.
IoT Device Communication: Smart sensors often report data that triggers automated actions. By requiring each sensor to sign its data packets, the system prevents “spoofing,” where a malicious actor sends fake data (like a false temperature reading) to trigger an unauthorized system shutdown.
Common Mistakes
Even with robust cryptography, the human element often introduces vulnerabilities. Avoiding these common mistakes is crucial for maintaining system integrity.
- Poor Key Management: Storing private keys in plaintext or on internet-connected devices is the most frequent cause of security breaches. If a private key is stolen, the attacker can effectively “become” the user.
- Ignoring Replay Attacks: If a system does not include a unique nonce (or sequence number) in every transaction, an attacker can capture a valid signed transaction and re-submit it multiple times to double-spend or duplicate an action.
- Weak Entropy (Randomness): Cryptographic signatures rely on random number generation to create keys. If the random number generator is predictable, an attacker can derive the private key from the public key, rendering the entire system useless.
- Lack of Timestamping: Without a reliable timestamp embedded in the signature, it is difficult to prove the order of operations, which can lead to conflicts in distributed systems.
Advanced Tips
To take your implementation to a professional level, consider these advanced cryptographic strategies:
Multi-Signature (Multisig) Wallets: Instead of relying on a single private key, require multiple keys to authorize a transaction. For example, a “2-of-3” setup requires two out of three authorized parties to sign off on a transaction. This drastically reduces the risk of a single point of failure.
Threshold Signature Schemes (TSS): TSS is a more advanced version of multisig. Instead of multiple signatures being stored on the ledger, the participants perform a distributed computation to generate a single valid signature. This is faster, more private, and consumes less space on the ledger.
Hardware Security Modules (HSMs): For enterprise-grade security, never let the application code handle private keys. Use an HSM—a physical device designed to manage and perform cryptographic operations—to ensure the private key never leaves the secure hardware.
Conclusion
The requirement for a cryptographic signature is the primary defense against the chaos of digital manipulation. By forcing every transaction to be tied to a specific private key, we create a system where reputation is earned, data is immutable, and accountability is absolute.
As you move forward in designing or auditing digital systems, remember that security is not a “set it and forget it” feature. It requires strict adherence to key management, the use of unique nonces to prevent replay attacks, and a commitment to decentralized verification. When every entry is signed, the integrity of the entire system is guaranteed by the laws of mathematics rather than the fallibility of human administrators.
Leave a Reply