The Architecture of Digital Resilience: Advanced Hosting Security for High-Growth Enterprises
In the modern digital economy, your infrastructure is not merely a utility—it is your most significant attack surface.
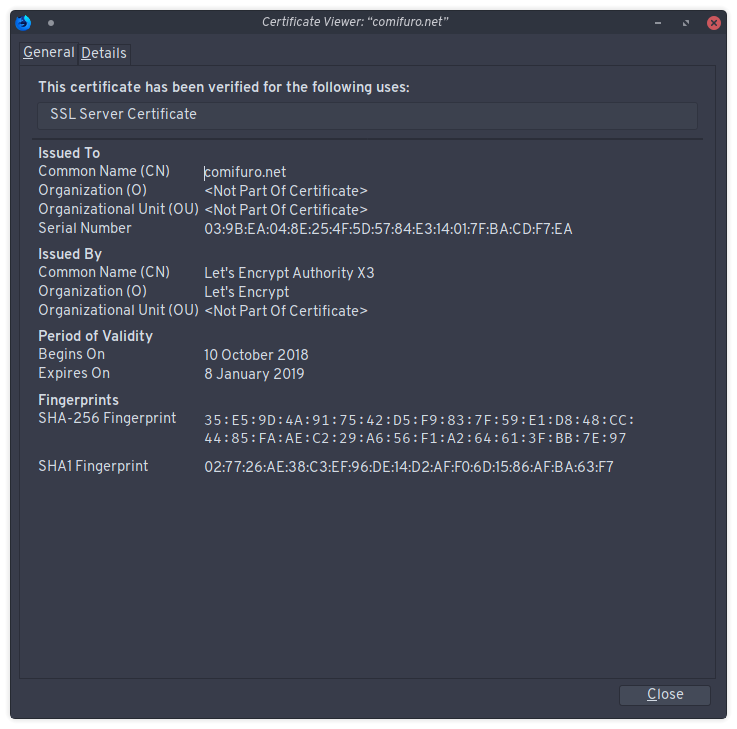
Most business leaders treat hosting security like a home security system: they lock the front door (SSL) and perhaps install a motion sensor (a basic firewall), assuming they are protected. But in the current threat landscape, where automated botnets and AI-driven reconnaissance are the new baseline, that level of security is akin to leaving the back window open in a neighborhood full of cat burglars.
Security is not a checkbox; it is a competitive advantage. If your infrastructure experiences downtime, data exfiltration, or a breach of trust, you are not just losing revenue—you are eroding the brand equity you spent years building.
The Illusion of Managed Security
The core problem for most entrepreneurs and decision-makers is the “Managed Hosting Fallacy.” Many believe that if they pay for a premium managed hosting provider, their application security is a “solved” problem.
This is a dangerous misconception. Managed providers protect the *server-level* infrastructure and the hypervisor layer. They do not protect your application code, your vulnerable plugins, your weak API endpoints, or the human error inherent in your team’s workflows. When a breach occurs, the hosting provider points to the application logs, and you are left to manage the fallout.
In high-stakes environments—SaaS, Fintech, or e-commerce—security must be viewed through the lens of Defense in Depth. You are not looking for a single silver bullet; you are looking to build a multi-layered barrier that makes the cost of attacking you higher than the potential gain for the attacker.
The Anatomy of Modern Threats
To build a fortress, you must understand how the siege works. Today’s threat landscape is defined by three specific vectors:
* Credential Stuffing: Using stolen credentials from other breaches to gain unauthorized access to your admin panels.
* Supply Chain Attacks: Injecting malicious code into third-party dependencies (NPM packages, plugins, or API integrations) that your application relies upon.
* Zero-Day Exploits: Targeting unpatched vulnerabilities in the software stack (like CMS cores or server-side frameworks) before the official patch is even released.
If your hosting security strategy relies solely on a WAF (Web Application Firewall), you are vulnerable to application-logic attacks that bypass traditional perimeter defenses.
The “Zero-Trust” Hosting Framework
For high-performance organizations, I recommend adopting a Zero-Trust approach to infrastructure. This means assuming the perimeter has already been breached and designing your architecture accordingly.
1. Hardening the Perimeter (The Edge)
Do not allow direct traffic to your origin server. Utilize a Global Content Delivery Network (CDN) with integrated Web Application Firewalls.
* Strategy: Implement Geo-blocking and IP reputation filtering at the edge. If your business operates primarily in North America and Western Europe, there is often little reason to allow traffic from regions known for high-volume automated bot activity.
* Advanced Tactic: Use “Rate Limiting” on your login endpoints and search queries to prevent brute force and resource exhaustion attacks.
2. Application-Level Isolation
If you are running multiple applications or microservices, ensure they are logically and physically isolated.
* Containerization: Utilize Docker or similar container technologies to ensure that if one service is compromised, the attacker cannot easily pivot to the rest of your stack.
* Principle of Least Privilege (PoLP): Your application’s database user should only have the permissions necessary to function. Never use a “Root” or “Superuser” account to connect your web app to your database.
3. Automated Vulnerability Lifecycle Management
Security is dynamic. A system that is secure today may be vulnerable tomorrow because a new CVE (Common Vulnerabilities and Exposures) has been disclosed.
* The Framework: Implement a CI/CD pipeline that includes automated dependency scanning. Tools like Snyk or GitHub Advanced Security should be integrated to alert your team the moment a vulnerable library is detected in your build.
* The Edge Case: Never “patch in production.” Always test updates in a staging environment that mirrors your production infrastructure. If a plugin update breaks your payment gateway at 2:00 AM, you are experiencing a self-inflicted denial-of-service attack.
Common Mistakes That Sabotage Security
If you are running multiple applications or microservices, ensure they are logically and physically isolated.
* Containerization: Utilize Docker or similar container technologies to ensure that if one service is compromised, the attacker cannot easily pivot to the rest of your stack.
* Principle of Least Privilege (PoLP): Your application’s database user should only have the permissions necessary to function. Never use a “Root” or “Superuser” account to connect your web app to your database.
3. Automated Vulnerability Lifecycle Management
Security is dynamic. A system that is secure today may be vulnerable tomorrow because a new CVE (Common Vulnerabilities and Exposures) has been disclosed.
* The Framework: Implement a CI/CD pipeline that includes automated dependency scanning. Tools like Snyk or GitHub Advanced Security should be integrated to alert your team the moment a vulnerable library is detected in your build.
* The Edge Case: Never “patch in production.” Always test updates in a staging environment that mirrors your production infrastructure. If a plugin update breaks your payment gateway at 2:00 AM, you are experiencing a self-inflicted denial-of-service attack.
Common Mistakes That Sabotage Security
Even sophisticated teams often fall into the trap of “Security Through Obscurity”—believing that hiding their login pages or using non-standard ports will keep them safe. It won’t.
1. Ignoring Logs: If you aren’t analyzing your access and error logs, you are flying blind. An uptick in 404 errors or failed login attempts is an early warning system.
2. Weak Identity Management: SSH keys are superior to passwords, but if they aren’t rotated and protected with passphrases, they are just as vulnerable. Furthermore, if you are not using Multi-Factor Authentication (MFA) on *everything*—from your hosting dashboard to your server access—you are fundamentally insecure.
3. Backing Up to the Same Server: If your backups reside on the same server or the same environment as your live site, ransomware can encrypt both simultaneously. Always maintain an “Air-Gapped” or off-site immutable backup.
The Future: AI-Driven Security and Sovereign Infrastructure
As we move toward a future defined by AI, we are entering a phase of “Machine-on-Machine” security. Attackers are using AI to discover vulnerabilities at scale, which means your defense must be equally automated.
We are seeing a trend toward Serverless Architectures and Edge Computing, where the attack surface of the server is abstracted away entirely. By offloading your compute to ephemeral, event-driven functions, you remove the persistent target that attackers look for.
Furthermore, as data sovereignty regulations (like GDPR, CCPA, and others) become more stringent, the location and encryption of your data will shift from a “technical requirement” to a “legal liability.” Future-proofing your hosting means preparing for architectures that allow for regionalized data residency without sacrificing global performance.
Conclusion: The Mindset Shift
Security is not a finish line; it is a permanent state of high-alert operational excellence. The goal is to move from being a “soft target” to being a “hard target.” Attackers are rational actors; they want the path of least resistance. By hardening your infrastructure, implementing automated monitoring, and embracing a Zero-Trust mindset, you signal that your environment is not worth the effort.
Take an inventory of your current infrastructure this week. If you cannot explain exactly how your data is encrypted at rest, how your traffic is filtered, and what the recovery protocol is for a total catastrophic failure, you are currently operating on luck rather than strategy.
In the digital world, luck is not a business model. It’s a liability.
Leave a Reply