The Invisible Fortress: Balancing User-Friendly Design with Cryptographic Integrity
Introduction
In the digital age, users demand an experience that is as frictionless as a conversation. They expect instant logins, seamless transactions, and interfaces that require zero technical training. Yet, beneath this polished surface lies a volatile landscape of cybersecurity threats, data breaches, and complex regulatory requirements. The tension between a user-friendly frontend and a robust cryptographic backend is the defining challenge of modern software architecture.
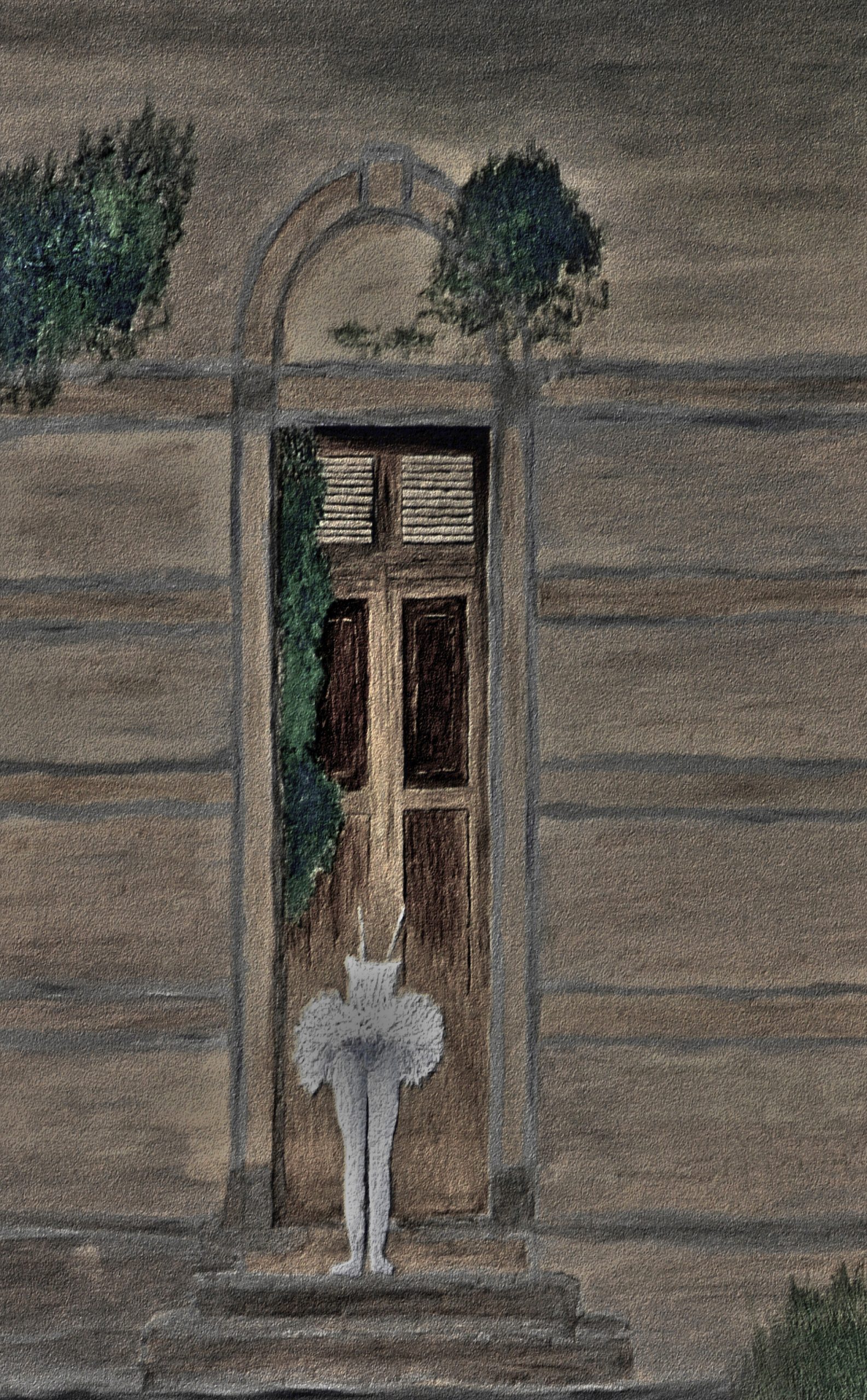
The goal is not to force users to choose between security and convenience. Rather, the goal is to create an “invisible fortress”—a system where high-level encryption and secure protocols act as the foundation for an effortless user experience. When done correctly, the user never notices the heavy lifting occurring in the background, yet they remain shielded by enterprise-grade protection.
Key Concepts
To bridge the gap between design and security, we must first define the two halves of the equation.
User-Friendly Design (The Facade): This encompasses the UX/UI layer. It focuses on cognitive load, accessibility, and speed. It is the part of the application that communicates trust through visual clarity, intuitive navigation, and responsive feedback.
Cryptographic Backend (The Fortress): This is the engine room. It involves end-to-end encryption (E2EE), hashing algorithms (like Argon2 or bcrypt), TLS/SSL protocols, and secure key management. Its primary role is to ensure data integrity and confidentiality, even if the outer shell is compromised.
The synergy between these two occurs at the abstraction layer. Developers must abstract away cryptographic complexity so that the user interaction remains simple. For instance, a user shouldn’t have to manage raw private keys; the system should handle key derivation behind the scenes while providing the user with a simple biometric authentication trigger.
Step-by-Step Guide: Designing Secure, Frictionless Systems
- Implement Transparent Encryption: Ensure data is encrypted at rest and in transit without requiring user intervention. Use modern libraries that handle key rotation automatically, so the user never has to reset their security settings manually.
- Prioritize Biometric-Backed Authentication: Replace cumbersome password requirements with FIDO2 or WebAuthn standards. This allows users to use their device’s built-in biometrics (FaceID, fingerprint) to sign cryptographic challenges, providing bank-grade security with a single touch.
- Standardize Error Messaging: Never reveal technical cryptographic failures to the user. If a decryption error occurs, provide a generic “Unable to process request” message. Detailed error logs belong in the backend for developers, not on the user’s screen.
- Use Asynchronous Processing: Cryptographic operations—such as signing large files or re-encrypting databases—can be slow. Use background queues to perform these tasks so the UI remains responsive, displaying progress indicators rather than freezing the application.
- Automate Security Lifecycle Management: Implement systems where security certificates and session tokens expire and renew automatically. This prevents the “security fatigue” that occurs when users are constantly prompted to re-authenticate.
Examples and Case Studies
The Banking App Paradigm: Modern digital banks have mastered the invisible fortress. When a user checks their balance, the app performs a handshake with the server using mutual TLS. While the user sees a simple dashboard, the app is actually validating cryptographic certificates, checking for root-access on the device, and encrypting the local cache. The user experiences a 200ms load time, while the backend processes thousands of security checks.
Messaging Platforms: Apps like Signal demonstrate how to design for the non-technical. The user simply sends a text message. Behind the scenes, the app automatically manages the Double Ratchet Algorithm. The user sees a “Message Delivered” checkmark, unaware that a new ephemeral key was generated and destroyed for that specific packet of information. This is the gold standard of hiding complexity.
Common Mistakes
- “Security through Obscurity”: Attempting to hide cryptographic logic by making the frontend code unreadable is not security. It confuses developers and creates technical debt without stopping a motivated attacker.
- Over-Prompting Users: Asking a user to confirm every single action with a password or MFA token destroys trust. Use “risk-based authentication” instead—only step up the security challenge when the system detects an anomaly (e.g., a new IP address or unusual behavior).
- Hardcoding Keys: Never store cryptographic keys in the frontend code or the client-side configuration. This is a catastrophic failure that renders the entire backend security moot.
- Ignoring UX in Security Flows: If a security process takes too long or is confusing, users will find “workarounds,” such as writing passwords on sticky notes or disabling security features. Secure design must be the path of least resistance.
Advanced Tips
To truly elevate your architecture, consider the implementation of Zero-Knowledge Proofs (ZKP). ZKP allows the backend to verify that a user possesses a credential (like a password or proof of age) without the system ever having to store or “know” that data. This removes the liability of storing sensitive user information, turning your database into a vault that holds nothing of value to a hacker.
True security is not about building walls that are hard to climb; it is about building systems where the user is instinctively guided toward safe behavior without ever feeling restricted by the architecture.
Additionally, focus on Hardware Security Modules (HSM) or Trusted Execution Environments (TEE). By offloading the most sensitive cryptographic operations to the device’s dedicated security chip, you ensure that even if the mobile operating system is compromised, the primary keys remain physically isolated and inaccessible to malicious software.
Conclusion
The contrast between user-friendly design and a cryptographic backend is not a conflict to be resolved, but a partnership to be cultivated. By abstracting complexity, leveraging modern authentication standards, and prioritizing the user’s cognitive load, you can build applications that are both impenetrable and delightful to use.
The most successful products of the next decade will be those that treat security as a fundamental feature of the user experience rather than an afterthought. When you hide the fortress, you don’t just protect your users—you empower them to interact with your digital environment with total confidence.
Leave a Reply