Outline
- Introduction: The paradox of self-custody and the danger of centralized recovery.
- The Core Problem: Why Centralized Recovery Agents (CRAs) negate the benefits of decentralization.
- Key Concepts: Understanding Threshold Cryptography, Shamir’s Secret Sharing (SSS), and Multi-Party Computation (MPC).
- Step-by-Step Guide: Implementing a decentralized recovery protocol.
- Real-World Applications: How decentralized finance (DeFi) and institutional custody are shifting toward social recovery.
- Common Mistakes: The “single point of failure” traps.
- Advanced Tips: Geographic distribution and hardware heterogeneity.
- Conclusion: Balancing security with sovereignty.
The Decentralization Paradox: Why You Must Eliminate Centralized Recovery Agents
Introduction
The core promise of blockchain technology and decentralized systems is autonomy—the ability to act as your own bank, your own notary, and your own security firm. However, this autonomy comes with a heavy burden: the “Key Management Dilemma.” When you lose your private keys, you lose your assets. For years, the industry’s answer was the Centralized Recovery Agent (CRA)—a third party that holds a piece of your key or a master override to restore access.
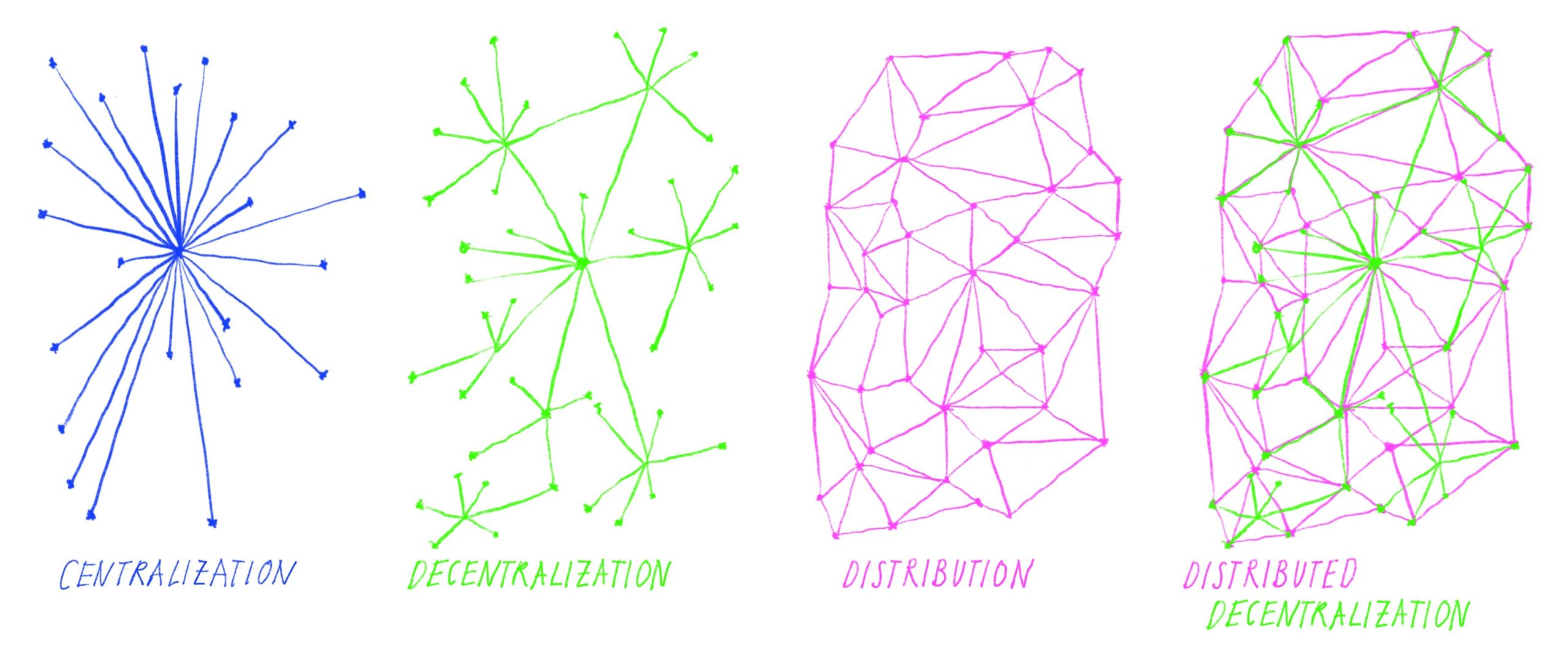
But here is the hard truth: if a third party has the power to restore your access, they also have the power to seize it. By relying on centralized recovery, you are effectively re-introducing the very counterparty risk that decentralization was built to solve. To maintain the ethos of true ownership, we must move toward decentralized, trustless recovery mechanisms that keep control strictly in the hands of the user.
The Core Problem
A Centralized Recovery Agent is a single point of failure by design. Whether it is a cloud provider, a centralized exchange, or a specialized recovery service, the moment you grant them a role in your key management, you change the nature of your security model from trustless to trusted.
“If you can be prevented from accessing your assets by the decision of a board of directors, a government subpoena, or a hacked server at a service provider, you do not truly own your keys.”
When we use CRAs, we are essentially building a gatekeeper. If the agent becomes compromised or malicious, the security of your entire system collapses. To achieve true self-sovereignty, the recovery mechanism must be mathematically distributed, ensuring that no single entity—not even the software provider—holds the keys to your kingdom.
Key Concepts: The Architecture of Trustless Recovery
To avoid centralization, we must rely on cryptographic primitives that allow for recovery without a central authority. These are the three pillars of decentralized security:
Shamir’s Secret Sharing (SSS)
SSS allows a secret (your private key) to be divided into multiple “shares.” These shares are distributed among various guardians. The secret can only be reconstructed if a predefined number of shares (a threshold) are brought together. For example, in a 3-of-5 scheme, any three guardians can restore the key, but two or fewer cannot.
Multi-Party Computation (MPC)
MPC takes the concept further. Unlike SSS, where the private key might be reconstructed in a single location during the recovery process, MPC allows the key to be used to sign transactions without the full key ever existing in one place. The computation is performed collaboratively by independent nodes, keeping the private key fragments cryptographically separated at all times.
Social Recovery Wallets
This is a human-centric application of threshold cryptography. Instead of relying on a corporation, you designate friends, family members, or independent hardware devices as “guardians.” If you lose access, your guardians coordinate to authorize a key reset. The key never leaves your control; the guardians only provide a digital signature to approve the change of ownership.
Step-by-Step Guide: Implementing a Decentralized Recovery Protocol
Moving away from centralized agents requires a shift in how you structure your backup infrastructure. Follow this protocol to ensure your recovery is truly decentralized.
- Define Your Threat Model: Determine what you are protecting against. Is it physical loss of a device, fire/theft of a location, or malicious intent? This dictates your threshold (e.g., 2-of-3 for convenience, 3-of-5 for high security).
- Select Decentralized Guardians: Choose a mix of entities that do not share a common failure point. This should include a combination of personal hardware devices, trusted individuals, and perhaps a geographically distinct storage location.
- Generate Key Fragments: Use a reputable, open-source library to split your master seed or private key. Ensure this generation occurs in an air-gapped environment to prevent digital interception.
- Distribute Shares Securely: Provide each guardian with their unique share. Use physical media (like stainless steel plates) for long-term cold storage, or encrypted cloud silos for more accessible fragments.
- Periodic Audits: Every six months, verify that your guardians still have their shares and that your recovery software remains compatible with current blockchain standards.
Examples and Case Studies
The shift toward decentralized recovery is already transforming the landscape for both individuals and institutions.
The Social Recovery Model: Projects like the Argent wallet have pioneered social recovery. By allowing users to designate a set of “guardians”—which can be other wallets or a decentralized identity provider—users can recover access to their funds if their primary device is stolen. The wallet provider itself has no technical ability to access the funds, fulfilling the decentralization mandate.
Institutional MPC Custody: High-net-worth platforms like Fireblocks or Gnosis Safe have moved toward threshold-based custody. Rather than a single “master key” held by the CEO, institutional access requires a quorum of signatures from different departments or geographical offices. This eliminates the risk of an “insider job” or a single hacked server compromising the entire treasury.
Common Mistakes: The “Single Point of Failure” Traps
Even when attempting to be decentralized, users often fall into traps that re-introduce centralization.
- The “Co-Location” Mistake: Storing all your backups in one physical location (e.g., a home safe). If the house burns down or the safe is stolen, your decentralization efforts are moot.
- Dependency on Proprietary Software: Using a recovery scheme that only works if a specific company exists. If that company goes bankrupt, your “decentralized” backup is useless because the recovery tool is proprietary and closed-source.
- Over-Trusting Digital Guardians: Relying on email-based or SMS-based recovery codes. These are highly susceptible to SIM-swapping and account takeovers, effectively acting as a centralized “backdoor” that bypasses your security.
Advanced Tips
To harden your decentralized recovery, consider these advanced strategies:
Geographic Heterogeneity: Ensure your fragments are stored in different legal jurisdictions. This protects against localized legal actions or catastrophic natural disasters. If you have five shards, ensure they are spread across at least three different countries.
Hardware Heterogeneity: If you use hardware wallets as part of your recovery threshold, do not use the same brand for all shards. If a specific vulnerability is discovered in the firmware of Brand A, you want your recovery threshold to remain intact via the hardware of Brand B.
Timelock-Enabled Recovery: For advanced users, implement a “timelock” on your recovery process. This allows you a window of time to cancel a recovery attempt if a malicious actor tries to spoof your identity. It creates a buffer between the request for recovery and the actual transfer of control.
Conclusion
Decentralization is not just about the technology; it is about the distribution of power. By outsourcing your recovery to a centralized agent, you are essentially choosing convenience over sovereignty. While the path of true self-custody requires more diligence and planning, it is the only way to ensure that your digital assets remain yours, regardless of the actions of third-party intermediaries.
By leveraging threshold cryptography, geographically diverse storage, and open-source recovery tools, you can build a system that is both resilient to loss and immune to censorship. Take the time to audit your current backup strategy today. If your recovery process relies on a “Forgot Password” link or a centralized support desk, you haven’t yet achieved the freedom that blockchain was designed to provide.
Leave a Reply