The Future of Trust: Reputation Scores and Decentralized Identifiers (DIDs)
Introduction
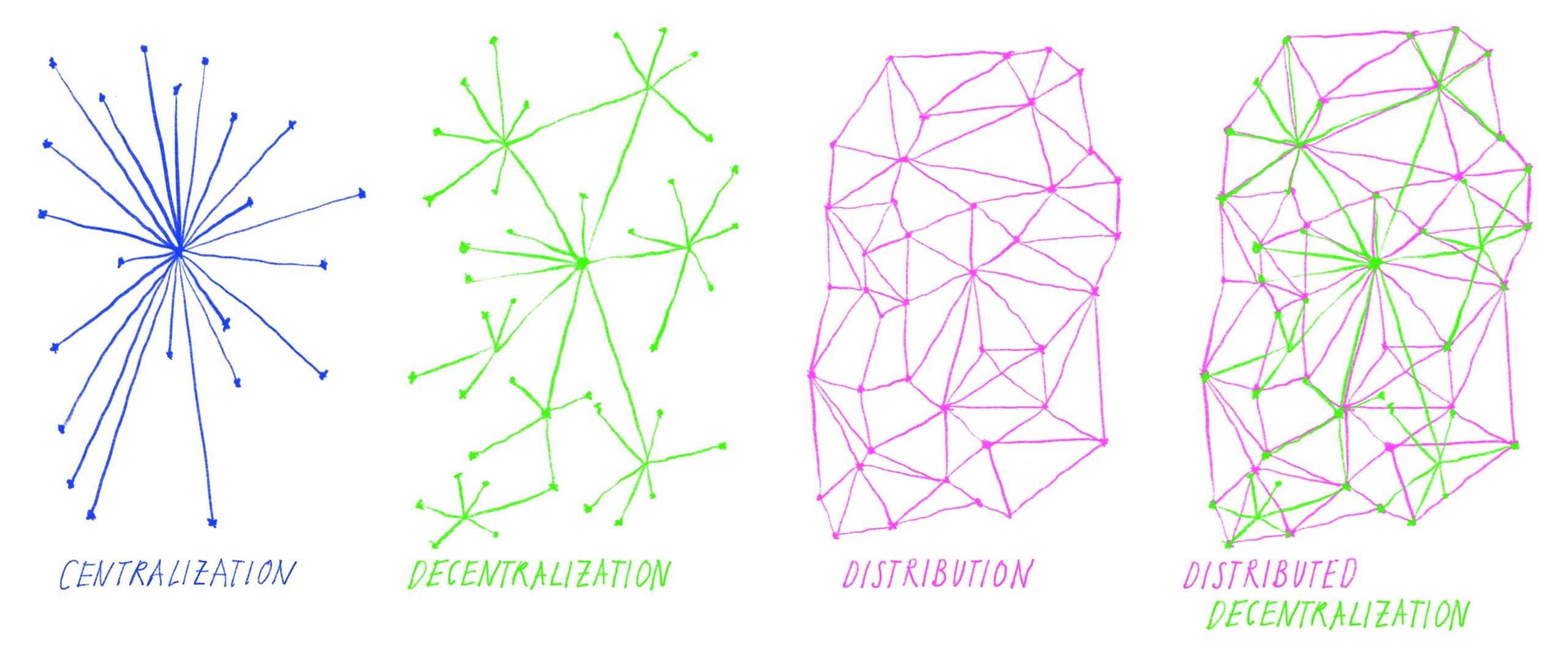
In the traditional digital landscape, your reputation is siloed. It lives inside the databases of platforms like eBay, LinkedIn, or credit bureaus. You do not own this data; you merely rent it. If a platform decides to ban you or go out of business, your years of building trust vanish instantly. This paradigm is shifting toward a user-centric model where reputation scores are stored as encrypted metadata linked to unique Decentralized Identifiers (DIDs).
By decoupling your reputation from specific platforms, you regain control over your digital identity. This article explores how DIDs and encrypted metadata are creating a portable, verifiable, and privacy-preserving layer of trust that functions across the entire internet.
Key Concepts
To understand the mechanics of decentralized reputation, we must first define the core components: DIDs and Encrypted Metadata.
Decentralized Identifiers (DIDs)
A DID is a new type of identifier that enables verifiable, decentralized digital identity. Unlike a username or email address, a DID is not issued by a central authority. It is a URI (Uniform Resource Identifier) that points to a DID Document, which contains cryptographic keys used to prove ownership of the identity. Think of a DID as a digital “passport” that you carry with you, independent of any single service provider.
Encrypted Metadata as Reputation
Reputation is essentially a collection of claims made about an entity—your transaction history, community contributions, or professional certifications. When these claims are stored as encrypted metadata linked to your DID, they become portable. Because the data is encrypted, the user chooses exactly who can see it and when. You can prove you have a “high reputation score” without revealing the granular details of every transaction that led to that score.
Step-by-Step Guide: Implementing Decentralized Reputation
- Establish your DID: Use a digital wallet or identity provider that supports W3C DID standards. Upon creation, a public-private key pair is generated. Your public key is broadcast to a ledger (like a blockchain or a distributed ledger), while the private key remains on your device.
- Request Attestations: Interact with service providers to earn reputation. When you complete a task—such as paying a loan on time or contributing code to an open-source project—the platform issues a “Verifiable Credential” (VC) signed by their DID.
- Store Metadata Securely: These credentials represent your reputation. They are stored in your encrypted digital wallet. The metadata is encrypted using your public key, meaning only you can decrypt the contents or authorize others to access specific portions.
- Present Proofs: When you need to demonstrate your reputation (e.g., applying for a decentralized loan), you generate a “Zero-Knowledge Proof” (ZKP). This allows you to verify that your score meets a certain threshold without disclosing the underlying data points that calculated it.
- Revocation and Update: As your reputation grows, you receive updated credentials linked to your DID. Because the ledger tracks the validity of the issuer’s key, the system can instantly verify if your reputation is current or if an issuer has revoked a credential.
Examples and Real-World Applications
The application of DID-linked reputation extends far beyond simple user profiles. It creates new possibilities for trust-based economies.
Decentralized Finance (DeFi)
Current DeFi lending is often over-collateralized because there is no way to verify a borrower’s creditworthiness. By using a DID, a borrower can share an encrypted “Credit Score” credential derived from their history across multiple protocols. This allows for under-collateralized loans based on verified past behavior, opening up financial inclusion to millions.
Professional Credentialing
Imagine a job application where you don’t send a PDF resume. Instead, you provide a link to your DID. An employer can verify, in real-time, that your university issued your degree and that your previous employer verified your employment dates. The metadata is encrypted, so you only reveal the specific certifications required for the role, keeping your full work history private.
Collaborative Marketplaces
Freelance platforms currently lock users into their ecosystem. With decentralized reputation, a freelancer can carry their “five-star rating” from one platform to another. If they move to a new, lower-fee marketplace, they bring their verified history with them, lowering the barrier to entry and fostering healthy competition between platforms.
Common Mistakes
- Storing Sensitive Data on-chain: A common error is confusing the DID ledger with a database. You should never store PII (Personally Identifiable Information) directly on a public blockchain. Only the cryptographic hash or the pointer to the encrypted data should be stored publicly.
- Ignoring Key Management: If you lose the private key linked to your DID, you lose your reputation. Many users fail to implement robust social recovery or multi-signature backup solutions, leading to the permanent loss of their digital identity.
- Over-sharing Credentials: Users often provide full access to their encrypted metadata when only a partial proof is required. Relying on Zero-Knowledge Proofs is essential to maintain privacy; sharing raw data is a significant security risk.
- Trusting Single Issuers: Relying on a single entity to build your entire reputation score creates a “decentralized” version of the same monopoly problems we face today. A healthy reputation should be a composite of scores from multiple, diverse issuers.
Advanced Tips
To truly master decentralized identity, you must look beyond the basic implementation.
Leverage ZK-SNARKs: To maximize privacy, use Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge (ZK-SNARKs). These allow you to prove a statement—such as “I have a reputation score greater than 800″—without revealing the score or the identity of the entities that provided the data. This is the gold standard for privacy-preserving reputation.
Implement Multi-Signature Recovery: Treat your DID as a high-value asset. Use a multi-signature wallet setup where you split your recovery shards among trusted friends or institutional custodians. This ensures that even if your primary device is lost or compromised, your reputation remains recoverable.
Contextual Reputation: Your reputation is not a single number. Build your DID ecosystem so that you have different “contexts.” You might have a professional DID for work, a financial DID for banking, and an anonymous DID for social platforms. Keeping these contexts distinct prevents unwanted correlation of your data while allowing you to maintain high reputation scores in each category.
Conclusion
The integration of reputation scores with Decentralized Identifiers represents a fundamental shift in how we establish trust online. By moving from platform-owned databases to user-owned, encrypted metadata, we empower individuals to take their reputation wherever they go. While the technology is still maturing, the path forward is clear: privacy-preserving, interoperable, and verifiable identity is the backbone of the next generation of the internet.
To start, focus on securing your DID and exploring platforms that support verifiable credentials. As you begin to collect attestations, you will find that your digital identity becomes a powerful asset that you—and only you—control.
Leave a Reply