Reputation Systems and Cryptographic Proofs: The Future of Trust
Introduction
In the digital age, trust is the most valuable currency. Whether you are hiring a freelancer, booking a rental property, or participating in a decentralized finance protocol, you rely on reputation systems to gauge reliability. However, traditional systems are often siloed, opaque, and prone to manipulation. You have no way to verify if a five-star review is genuine or if the “reputation” shown on a platform was artificially inflated.
The convergence of reputation systems and cryptographic proofs is changing this paradigm. By utilizing mathematical verification rather than blind faith in a centralized authority, we can create portable, immutable, and objective records of social and professional interactions. This article explores how cryptographic proofs turn subjective social history into verifiable data, creating a more honest digital economy.
Key Concepts
At its core, a reputation system using cryptographic proofs moves trust from institutions to mathematics. To understand this, we must define three foundational concepts:
Digital Identity and Self-Sovereignty
Traditional reputation is tied to an account (e.g., your LinkedIn profile). If the platform decides to ban you, your reputation vanishes. Cryptographic reputation links your history to your private keys. You own the identity, and the reputation follows you across different applications.
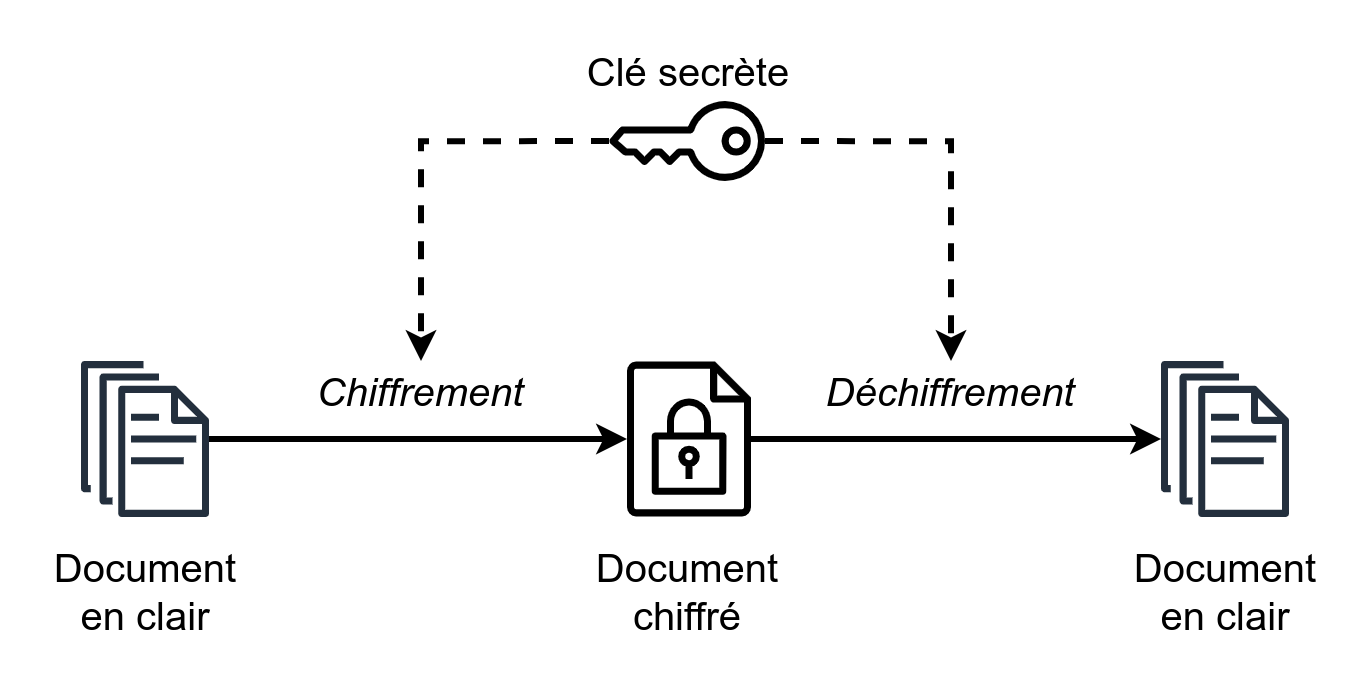
Cryptographic Proofs (Zero-Knowledge and Digital Signatures)
These are the mechanisms that prove an event occurred without exposing sensitive data. For example, a digital signature proves that a specific entity verified your work, while Zero-Knowledge Proofs (ZKPs) allow you to prove that you hold a certain reputation score without revealing the underlying transactions that built it.
On-Chain Attestations
An attestation is a signed statement. When a client pays a freelancer, the smart contract or the client’s wallet can sign a transaction that acts as a “proof of service.” This data is recorded on a distributed ledger, making it tamper-proof and verifiable by anyone with the public key.
Step-by-Step Guide: Implementing Cryptographic Reputation
Building a reputation system that relies on cryptographic proof requires a shift in how you architect user interactions. Follow these steps to integrate verifiable trust into your workflow:
- Define the Interaction Lifecycle: Identify the specific touchpoints where trust is established. This could be the completion of a project, the delivery of a product, or a peer-to-peer endorsement.
- Issue Cryptographic Attestations: Instead of storing a “rating” in a local database, create a smart contract or a decentralized identity (DID) structure that issues a signed statement upon task completion. This statement includes the metadata of the interaction (the “what,” “when,” and “who”).
- Aggregate Data via Verifiable Credentials: Use standards like W3C Verifiable Credentials to bundle these attestations. This allows users to store their reputation in a digital wallet, independent of any single platform.
- Implement Verification Logic: Build a front-end interface that validates these proofs against the blockchain or decentralized ledger. When a user presents their credentials, the system checks the signature, confirms it was issued by a trusted entity, and updates the user’s reputation score in real-time.
- Incorporate Decay and Weighting: Reputation is not static. Implement logic where cryptographic proofs carry more weight if they are recent or if the issuer has a high reputation themselves (a “reputation of reputation” model).
Examples and Real-World Applications
The practical application of cryptographic reputation extends far beyond simple star ratings. Here is how it is being applied today:
“Cryptographic proofs allow us to transform reputation from a vanity metric into a verifiable asset that can be used to collateralize loans, grant access to exclusive communities, or streamline hiring.”
Decentralized Freelance Marketplaces
Platforms like Braintrust or TalentLayer utilize on-chain attestations. When a developer completes a project, the client signs a cryptographic transaction. This developer can then take that proof to any other platform to demonstrate their actual performance history, preventing “platform lock-in.”
DeFi Credit Scoring
In decentralized finance (DeFi), under-collateralized lending is difficult because there is no traditional credit history. Cryptographic reputation allows users to prove their history of on-time loan repayments across multiple protocols. By presenting these proofs, they can qualify for lower interest rates or higher borrowing limits without revealing their identity to the entire network.
Sybil-Resistant Governance
In DAOs (Decentralized Autonomous Organizations), voting power is often manipulated by “Sybil attacks”—one person creating hundreds of accounts to sway a vote. Cryptographic reputation systems verify that an account belongs to a human who has a history of active, verified participation, effectively filtering out bots and bad actors.
Common Mistakes
Transitioning to a cryptographically verified system is complex. Avoid these pitfalls to ensure your implementation remains robust:
- Over-relying on Centralized Oracles: If your reputation system depends on a single server to verify data before it is “proved,” you have not actually decentralized trust. You have simply added a layer of complexity to a centralized system.
- Ignoring Data Privacy: Forcing users to reveal every transaction history to prove their reputation is a privacy nightmare. Use Zero-Knowledge Proofs to prove that a condition is met (e.g., “I have completed more than 10 projects”) without revealing the specific details of those projects.
- Static Reputation Models: Reputation is dynamic. A common mistake is treating a proof as a permanent status. Always implement expiration or “decay” mechanisms to ensure that a reputation built five years ago doesn’t carry the same weight as a recent interaction.
- Ignoring User Experience (UX): Cryptography is hard. If your system requires users to manage complex key pairs or understand gas fees for every interaction, adoption will fail. Hide the technical complexity behind intuitive wallet interfaces.
Advanced Tips
To take your reputation system to the next level, consider these advanced strategies:
Implement Recursive Proofs: As users accumulate thousands of interactions, verifying every single proof becomes computationally expensive. Use recursive ZKPs to verify the validity of a previous proof, essentially “rolling up” a long history into a single, compact proof of integrity.
Cross-Chain Portability: Ensure your reputation data is not trapped on a single blockchain. Use cross-chain messaging protocols to allow a reputation earned on one network (like Ethereum) to be verified and recognized on another (like Polygon or Solana).
Weighted Trust Networks: Not all proof issuers are equal. Implement a system where the “reputation of the issuer” modifies the weight of the proof. A proof of performance signed by a globally recognized organization should carry significantly more weight than a proof signed by an anonymous peer.
Conclusion
Reputation systems built on cryptographic proofs represent the next evolution of digital trust. By replacing the fallible “trust us” of centralized platforms with the mathematical certainty of cryptographic signatures and Zero-Knowledge Proofs, we create a more meritocratic and portable digital landscape.
For the individual, this means owning your history and your value. For the digital economy, it means reducing fraud, mitigating Sybil attacks, and enabling seamless interactions between parties who have never met. As these technologies mature, we can expect reputation to move from a siloed marketing tool to a fundamental layer of the internet’s infrastructure. Start small by integrating verifiable attestations into your workflows, and you will be at the forefront of this trust-based revolution.
Leave a Reply